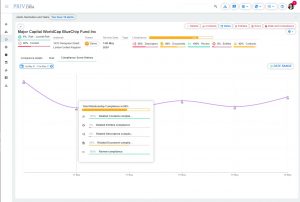
Compliance Score History
Meeting KYC (Know Your Customer) obligations plays a crucial role in building trust with clients. The better you know your customers, the more compliance score

Multi-factor authentication (MFA; encompassing Two-factor authentication or 2FA, along with similar terms) is an electronic authentication method in which a user is granted access to PRIV.DRM only after successfully presenting two pieces of evidence (or factors) to an authentication mechanism: knowledge (something only the user knows), possession (something only the user has), and inherence (something only the user is). MFA protects the user from an unknown person trying to access PRIV.DRM data .
A third-party authenticator (TPA) app enables two-factor authentication, showing a randomly-generated and constantly refreshing code to use for authentication.
Passwords can be forgotten, stolen, or compromised. This can result in being locked out of your account in addition to the loss of your data or impersonation.
Once you set up the two-factor authentication, you will enter your username and password, then, instead of immediately gaining access, you will be required to enter the code provided by one of the suggested authenticators.
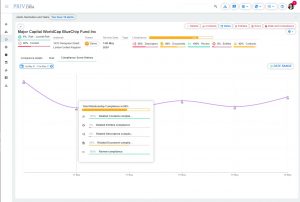
Meeting KYC (Know Your Customer) obligations plays a crucial role in building trust with clients. The better you know your customers, the more compliance score
How does KYC work? KYC (Know Your Contact in PRIV.DRM) is a significant element in establishing customers’ identities and understanding the nature of their activities.
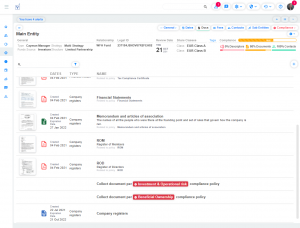
Documents in Privdrm? Know Your Client (KYC) procedures are a critical function in establishing customers’ identities and understanding the nature of their activities. In PrivDRM, we implemented
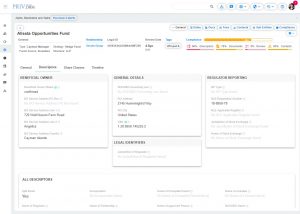
Logical grouping for descriptors The descriptors are a core feature of PRIV.DRM. They can be a part of the compliance process, risk review, risk assessment,

What do we offer? On the Help Port, we will provide you with quick information in the form of Frequently Asked Questions – FAQ Help